The coordination layer
between detection
and action
Director ingests NetFlow and sFlow data from your existing routers, detects attack conditions, and executes configurable multi-tiered response workflows automatically. On its own or as the traffic steering intelligence behind a full RioRey hybrid deployment.
Off-ramp scrubbing without the traditional barriers
In-line protection requires your DDoS mitigation appliance to sit directly in the traffic path. Off-ramp protection uses Director to monitor your flows and redirect only the traffic that needs scrubbing. Lower hardware costs, no single point of failure in the traffic path, and coverage across multiple ingress points.
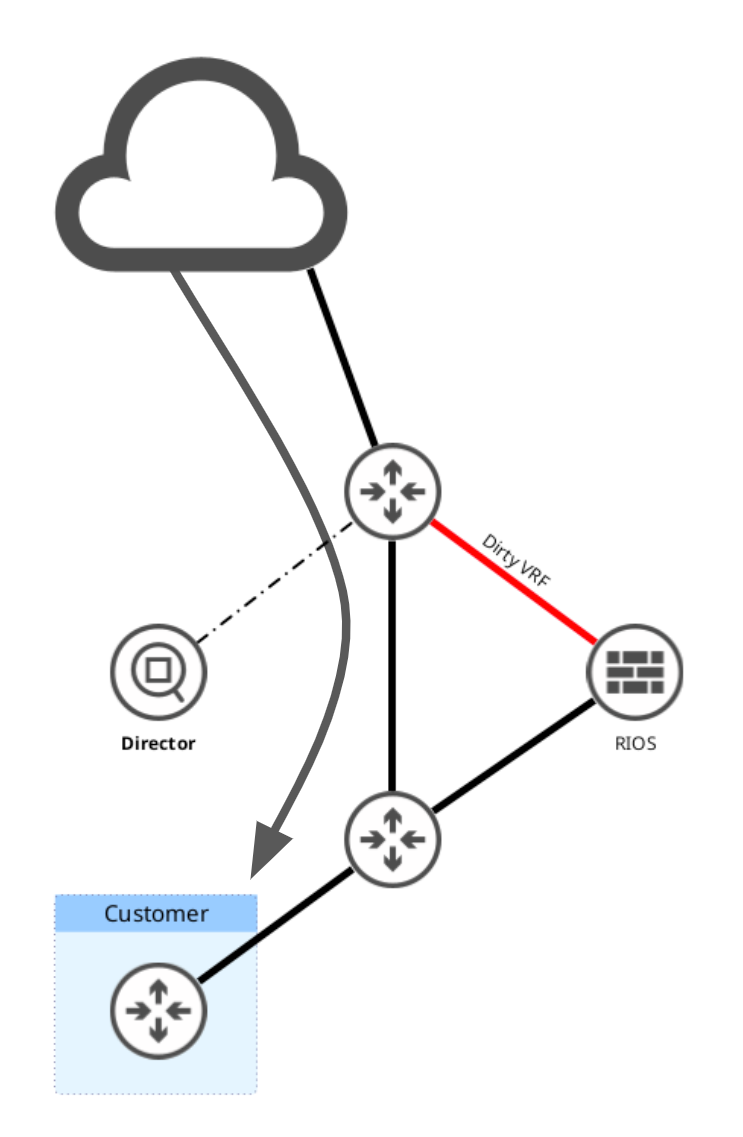
Traffic flows directly from upstream to the customer network. Director is continuously ingesting NetFlow data from the router and monitoring for anomalies. RIOS scrubbing hardware is standing by but not in the traffic path. No latency penalty, no unnecessary overhead.
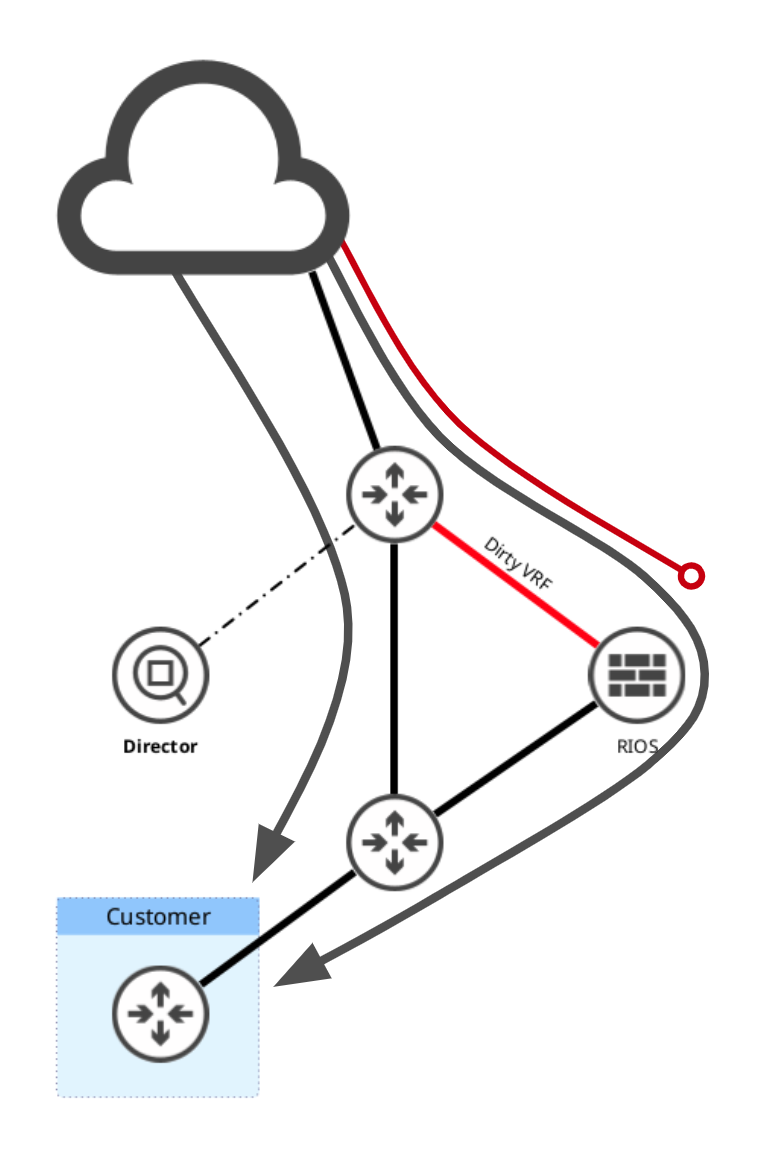
Director identifies an attack condition against a specific victim IP. It triggers a BGP announcement to pull only that victim's traffic through the RIOS scrubbing device. Clean traffic is returned to the network via GRE tunnel. Non-victim traffic is unaffected and continues to route normally.
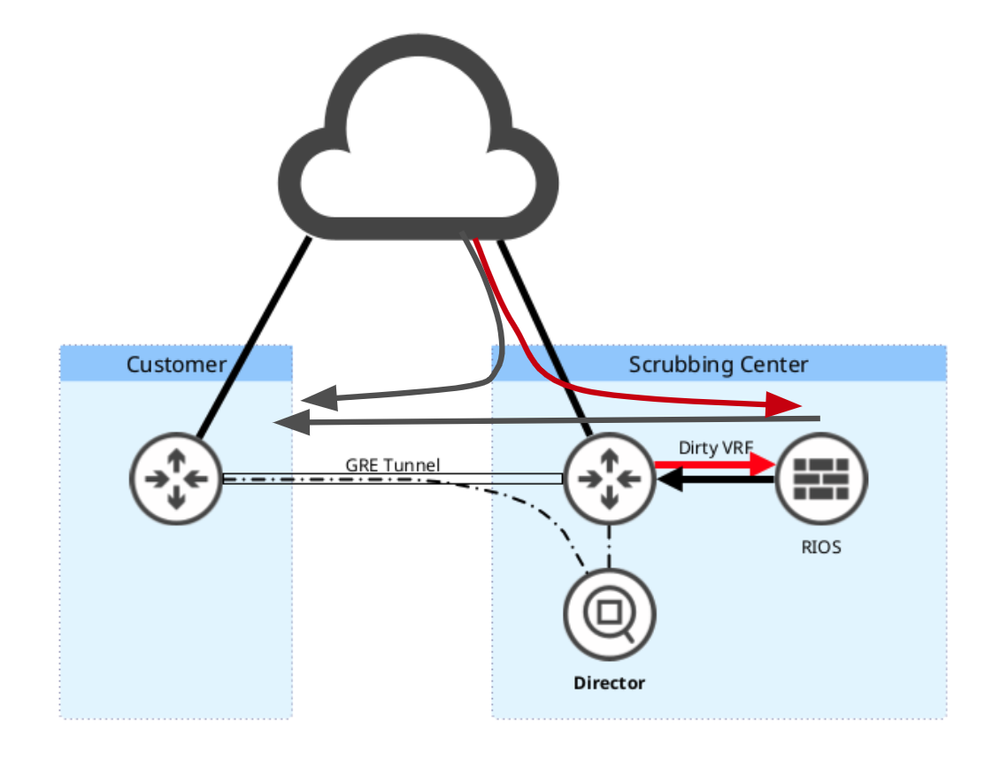
Director can remotely ingest flow data from a client's router outside your network. When an attack is detected, it triggers BGP redirection into your scrubbing center via GRE tunnel. Clean traffic returns to the client. rWeb provides each client with their own segmented reporting and access portal, making this a complete multi-tenant managed service architecture.
From flow data to action, automatically
Director is a virtual machine instance. It does not sit in the traffic path. It watches, decides, and steers.
Director receives flow telemetry from one or more routers and switches on your network. No new sensors required.
Flow data is analyzed against your configured thresholds and zone definitions. When conditions are met, a workflow is triggered.
A configured escalation workflow fires. Tiered actions can include multiple sequential steps based on attack volume (PPS or Gbps).
BGP redirect to RIOS scrubbing, escalation to rCloud, RTBH null routing, BGP FlowSpec upstream, or ACL-based blocking via script.
When an attack subsides, Director triggers a time-based withdrawal of the BGP announcement. Traffic returns to normal ingress at your edge automatically. Operators can also do this manually if preferred.
Director is predictable by design. Unlike RIOS, it does not use adaptive algorithms. It applies your configured rules, thresholds, and escalation sequences exactly as written. Simple to operate, easy to audit.
Customers are not required to use Director. Those with existing NetFlow tools or who prefer manual BGP redirection can do so. Director is the recommended path for single-vendor simplicity and full rWeb integration.
Redirection policy at the zone level, not just the network level
Most hybrid and off-ramp deployments treat redirection as a binary: traffic is either being scrubbed or it is not. The entire network shifts when a threshold is crossed. That works for simple environments, but it leaves no room for nuance.
Director pulls your group and zone definitions directly from rWeb. Those groups and zones are defined by destination IP and subnets within your network, and they are already the basis for your reporting, access controls, and multi-tenant structure. Director lets you attach independent redirection workflows to each of them.
The result is policy-driven traffic management across your entire network, not a single emergency overflow switch.
- Zones defined once in rWeb are immediately available in Director. No duplication, no translation layer.
- Different zones can have different thresholds, different escalation sequences, and different permitted actions.
- rCloud can be reserved exclusively for high-value zones if capacity is a constraint.
- Zones that frequently attract large volumetric floods can be set to redirect at lower thresholds, preserving your local bandwidth for everything else.
- Multi-step escalations can redirect to a local off-ramp RIOS appliance first, then escalate to rCloud only if that capacity is exceeded.
rCloud is a subscription resource with defined bandwidth capacity per plan. If you are on a plan with a ceiling, you do not want a large attack against a low-priority zone consuming capacity that a critical zone may need.
Director lets you configure zone-level workflow actions that explicitly permit or exclude rCloud escalation. Low-value zones can be handled locally, or null-routed at the upstream, without ever touching your rCloud allocation.
- Zone A (critical infrastructure): escalate to rCloud if local RIOS exceeds capacity
- Zone B (dev / staging): RTBH null routing only, rCloud not permitted
- Zone C (general hosting): local RIOS scrubbing, no cloud escalation
Some zones are consistent targets. A DNS infrastructure zone or a major transit prefix may attract volumetric floods regularly. Letting those attacks build to your default threshold before redirecting means those attacks are consuming your local link capacity while Director waits.
Set a lower redirect threshold for known high-traffic zones. Director will act earlier on those prefixes, preserving your on-premise bandwidth for everything else.
- Standard zones: redirect at 10 Gbps sustained traffic
- High-traffic zone: redirect at 2 Gbps, protecting overall link headroom
- Result: rCloud handles the zone's load; local edge stays clean for other traffic
For operators running in-line RIOS appliances, Director can monitor link saturation rather than just PPS or Gbps. When link utilization reaches a defined level, Director triggers rCloud scrubbing for the victim prefixes, keeping your local infrastructure from being overwhelmed.
This creates a true tiered architecture: RIOS handles attacks within its capacity, and rCloud absorbs the overflow automatically, without operator intervention.
- Stage 1: attack detected, RIOS in-line mitigation active
- Stage 2: link saturation threshold crossed, Director triggers rCloud escalation
- Stage 3: attack subsides, Director withdraws BGP announcement, traffic returns to edge
Four primary configurations
Director is a virtual machine instance that adapts to your architecture. It is not tied to a specific topology.
RIOS appliances or VMs sit in-line at the edge. Director monitors link saturation and upstream conditions, triggering upstream BGP FlowSpec, RTBH, or provider-side actions when link capacity is at risk.
The traditional hybrid model. RIOS handles attacks within local capacity. Director monitors thresholds and automatically escalates volumetric attacks that exceed local headroom to rCloud scrubbing, then reverts when the attack subsides.
Traffic is not in-line under normal conditions. Director monitors flows and BGP-redirects victim traffic through RIOS scrubbing hardware when an attack is detected. Clean traffic is returned via GRE tunnel. Used for protecting IPs on the operator's own network.
Director remotely ingests flow data from external client routers. Attacks trigger BGP redirection into the operator's scrubbing center via GRE tunnel. rWeb provides each client with a segmented portal, enabling a fully multi-tenant managed DDoS protection service.
Director license tiers
Director is licensed as a virtual machine instance, priced by the calculated average sum of incoming and outgoing bandwidth inspected over a one-month period. Six tiers cover environments from 10 Gbps through 400 Gbps. Deployments above 400 Gbps are handled on a custom basis.
Pricing based on a 12-month commitment, paid monthly. Contact sales for alternative terms or enterprise volume pricing. Professional Services (installation, training, tuning, non-RIOS support) available at $250/hr with a 1-hour minimum.
| Part No. | License Level | Max Avg Inspected Traffic | Pricing |
|---|---|---|---|
| RRD-10 | Director10 Gbps | 10 Gbps average | Contact sales |
| RRD-40 | Director40 Gbps | 40 Gbps average | Contact sales |
| RRD-100 | Director100 Gbps | 100 Gbps average | Contact sales |
| RRD-200 | Director200 Gbps | 200 Gbps average | Contact sales |
| RRD-300 | Director300 Gbps | 300 Gbps average | Contact sales |
| RRD-400 | Director400 Gbps | 400 Gbps average | Contact sales |
* Average inspected traffic is the calculated average sum of incoming and outgoing bandwidth over a one-month period. For deployments above 400 Gbps, contact sales for custom licensing. Director is available as an add-on to existing RioRey RIOS deployments or as a standalone off-ramp management tool.
Ready to discuss your architecture?
Director sizing depends on your traffic volumes, topology, and how you intend to use it. Our team can help you determine the right license tier and deployment model.
